What is ISO 27001? Information Security Simply Explained | DICIS AG
What is ISO 27001?
ISO 27001 is an international standard for Information Security Management Systems, which organizations (companies, associations, clubs, authorities, etc.) use to reliably implement all data protection and information security requirements. It follows the same principles as Quality Management Systems like ISO 9001, the so-called “High Level Structure” of the ISO standard family. Management systems according to ISO 27001 are certifiable as part of an ISO certification. In this article, you will learn about the requirements of ISO 27001.
Why does ISO 27001 exist?
Information security and data protection are among the most important topics for organizations that want and need to professionalize themselves in the context of digitalization and digital transformation. ISO 27001 is based on a simple philosophy: information security and data protection must not be left to chance. There must be clear rules for,
- for example, who is allowed to create new users,
- who manages their role permissions,
- which specific behavioral guidelines users of IT systems must observe,
- at what intervals and with what methods IT security is checked, etc.
ISO 27001 follows the PDCA cycle logic familiar from quality management: Plan, Do, Check, Act. In German: Planen, Umsetzen, Messen und Verbessern (Plan, Implement, Measure, and Improve).
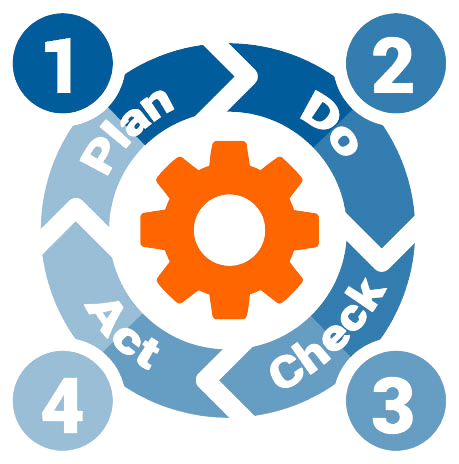
The PDCA cycle is also known from other management systems such as quality management. The structure of ISO 27001 is also similar to that of ISO 9001. Therefore, management systems from the areas of quality, environmental protection, or information security can be very well combined in the form of integrated management systems.
DICIS® AG offers a modern solution for ISO 27001 certification that significantly reduces the effort. With the help of an AI assistant, the entire documentation can be created within a few hours – instead of several weeks as before.
Companies can test the solution for 30 days free of charge and be guided step-by-step through the certification process.
How is ISO 27001 structured?
ISO 27001 follows the so-called High Level Structure and is similarly structured to ISO 9001 or ISO 14001. The actual requirements are in chapters 4 to 10. Additionally, there is an Annex with 93 controls that you must implement or justify to fully cover information security.
The standard is structured so that you can easily proceed step by step. You start by understanding your company, define rules, and ensure that work is done securely in everyday operations. Afterwards, you regularly check if everything is working and improve your system.
The following overview simply shows you what you specifically need to do in each chapter:
| Chapter | What you specifically need to do in this chapter |
|---|---|
| Chapter 4 – Context | Consider: Which data is important? What can happen? Where do you apply your security system? |
| Chapter 5 – Leadership | Ensure that the topic is important and everyone knows: data must be protected. |
| Chapter 6 – Planning | Consider: What can go wrong and how do we prevent it? |
| Chapter 7 – Support | Ensure that your employees know what to do and have the right resources. |
| Chapter 8 – Operation | Define how data is handled securely in daily operations. |
| Chapter 9 – Performance Evaluation | Regularly check: Is everything working or are there problems? |
| Chapter 10 – Improvement | If something is not working well, improve it step by step. |
| Annex A – Controls | Implement specific protective measures: rules, training, securing access, and protecting IT. |
DICIS® AG has developed an innovative and particularly simple path to ISO 27001 certification – especially for small businesses. Instead of complex projects and weeks of preparation, you use an AI-powered tool that guides you step-by-step through the implementation.
Through targeted questions, the system automatically identifies the relevant requirements and creates the necessary documentation in a short time. Certification then takes place efficiently via an online audit.
This makes ISO 27001 certification significantly easier and faster. You can start immediately and test the certification tool for 30 days free of charge now.
What do I need to implement in ISO 27001 Chapter 4.1 (Context of the Organization)?
In Chapter 4.1, ISO 27001 lays the foundation for an Information Security Management System to be implemented at all. Organizations create a list of relevant internal and external issues for this purpose.
- Internal issues: This involves addressing all areas where information security plays a role. For example: securing Wi-Fi, security of production facilities, data and information security in employees’ home offices, etc.
- External issues: This considers external influencing factors on information security. Create a list of issues that are relevant to you and your Information Security Management System. For example, new data protection regulations, security updates for your software, reports on cybercriminals’ attack strategies, or innovative security technologies.
ISO 27001 does not specify which internal and external issues you must monitor and analyze. Ultimately, it is a matter of relevance. At its core, however, it is quite simple. You need to clarify what potential threats exist, what regulations you must observe, and which areas of your organization are affected.
Which interested parties are relevant for ISO 27001?
When it comes to information security, different groups have different interests.
- Owners and investors seek the best possible protection for their invested capital, but also pay attention to the economic viability of a solution.
- Employees expect that implemented solutions
- are easy to use and
- do not restrict their productivity.
- The works council wants to ensure that records of employee activities are processed only for the purpose for which they were collected.
- Customers want clarity on how their data is processed and how their information is protected.
Countless other interested parties could be listed. ISO 27001 requires organizations to actively address these different interests and identify potential areas of tension that exist in information security management.
How do I define the scope (Chapter 4.3) of ISO 27001?
Contrary to a widespread assumption, ISO 27001 does not automatically have to be implemented for an entire organization. It is even conceivable that you implement ISO 27001 only for a few processes, for example, for all processes and activities related to the use of a CRM system (Customer Relationship Management system). Therefore, it is necessary to clearly define the scope of ISO 27001.
What do I need to do in Chapter 4.4 (The Information Security Management System)?
This chapter is the concretization of 4.3. Which processes and procedures does your ISMS cover? Create a list of all relevant processes and procedures for your ISMS. There are classic standard procedures that affect practically every organization: for example,
- creating and deleting internal users,
- expanding or restricting access rights,
- as well as the procedure for security flaws identified by management.
Here, ISO 27001 requires clear processes and procedures. With Innolytics AG’s digital Information Security Management System, you can meet these requirements quickly and easily.
What does ISO 27001 require from leadership? (Chapter 5.1)
Leaders play a special role within organizations. They are responsible for considering information security in all areas of daily work. They are the ones who define information security objectives, develop measures to implement them, and support employees in acquiring the necessary competencies. Chapter 5.1 explicitly lists the requirements for leaders in organizations.
What roles and responsibilities (Chapter 5.2) exist in ISO 27001?
ISO 27001, like all management systems, requires that there are fixed responsibilities and accountabilities for specific tasks. How these are structured in detail is not explicitly prescribed in the standard. However, it is important that roles and responsibilities are specifically named. It is therefore not enough to merely generally indicate that, for example, a certain department should think about information security. In an Information Security Management System (ISMS), specific individuals or functions are named.
What competencies do employees need regarding information security? (Chapter 7.3)
Organizations must ensure that the responsible persons have the necessary know-how to fulfill their tasks. At its core, this is a very logical requirement. What good is it if organizations set information security goals, develop measures, and appoint responsible persons, but then no one has the necessary expertise to carry this out?
What does information security assessment mean? (Chapter 8.2: Risk analysis and assessment)
ISO 27001 requires companies to regularly review their own IT infrastructure (which includes not only internal networks and devices connected to the internet, but also employees’ smartphones and even home workplaces in home offices). Everything can become an entry point for cybercriminals and thus represents a security risk.
ISO 27001 requires companies to regularly review their own IT infrastructure (this includes not only internal networks and internet-connected devices, but also employees’ smartphones and even home workstations). Everything can become a gateway for cybercriminals and thus represents a security risk.
ISO 27001 does not prescribe a specific form of risk analysis. However, there are security criteria listed in the standard. In addition, there are standards such as the BSI Standard that are compatible with ISO 27001.
What information security audits does ISO 27001 require (Chapter 9.2)?
- Internal audits are a central requirement of management systems, such as a Quality Management System according to ISO 9001:2015. What is it about?
- Audits are internal reviews that must be planned and conducted.
- The philosophy behind this is: if something is not regularly and systematically checked, it eventually falls out of focus and is ultimately forgotten.
However, precisely this form of negligence ultimately increases attack risks and can subsequently lead to damage.
How do I need to improve information security? (ISO 27001 Chapter 10.1)
ISO 27001 – like all certifiable standards in the ISO family – is based on the philosophy of “learning from mistakes.” Chapter 10.1 therefore establishes a binding approach to identified weaknesses and security flaws. They are intended to improve the overall system.
This list is not exhaustive. In practice, it is supplemented by security criteria. However, it provides a good overview of how the management system is structured and what requirements are placed on companies seeking ISO 27001 certification.




